In an era where data drives competitive advantage, organizations face a growing paradox: they must use more data to innovate, yet they must protect that same data more rigorously than ever before. Financial institutions, healthcare providers, governments, and technology firms all manage highly sensitive information that cannot be freely shared or exposed—even internally. Privacy-preserving computation platforms such as Duality are emerging as a credible and transformative solution, enabling organizations to compute on encrypted data without ever decrypting it.
TLDR: Privacy-preserving computation platforms like Duality enable organizations to analyze and process encrypted data without exposing sensitive information. By leveraging technologies such as homomorphic encryption and secure multi-party computation, these platforms preserve privacy while maintaining analytical utility. They address critical regulatory, security, and collaboration challenges across industries. As data privacy regulations tighten, encrypted computation is becoming a strategic necessity rather than an academic curiosity.
The traditional model of data processing requires decryption before analysis. This inherently creates risk. Once decrypted, information becomes vulnerable—to cyberattacks, insider threats, misconfigurations, or accidental leaks. The more systems that access raw data, the broader the attack surface becomes. With increasing regulatory scrutiny from frameworks such as GDPR, HIPAA, CCPA, and financial sector mandates, organizations are actively seeking architectures that minimize exposure while preserving computability.
Contents
- 1 The Core Idea: Computation Without Exposure
- 2 How Platforms Like Duality Work
- 3 Why This Matters Now
- 4 Industry Applications
- 5 Security Advantages Over Traditional Models
- 6 Performance and Practical Challenges
- 7 Strategic Implications for Enterprises
- 8 Comparing Approaches to Data Privacy
- 9 Building Trust in a Data-Driven Economy
- 10 The Road Ahead
The Core Idea: Computation Without Exposure
Privacy-preserving computation allows data to remain encrypted throughout its lifecycle—even while being analyzed. Technologies like Homomorphic Encryption (HE) make it mathematically possible to perform operations directly on encrypted values. Once computation is complete, only authorized parties can decrypt the final result.
In simple terms:
- Data is encrypted at the source.
- Computations are performed on ciphertext.
- Results are decrypted only by approved key holders.
- Raw data is never exposed during processing.
This approach fundamentally changes the security model. Instead of protecting data through perimeter defenses alone, encryption itself becomes the operating state of the information.
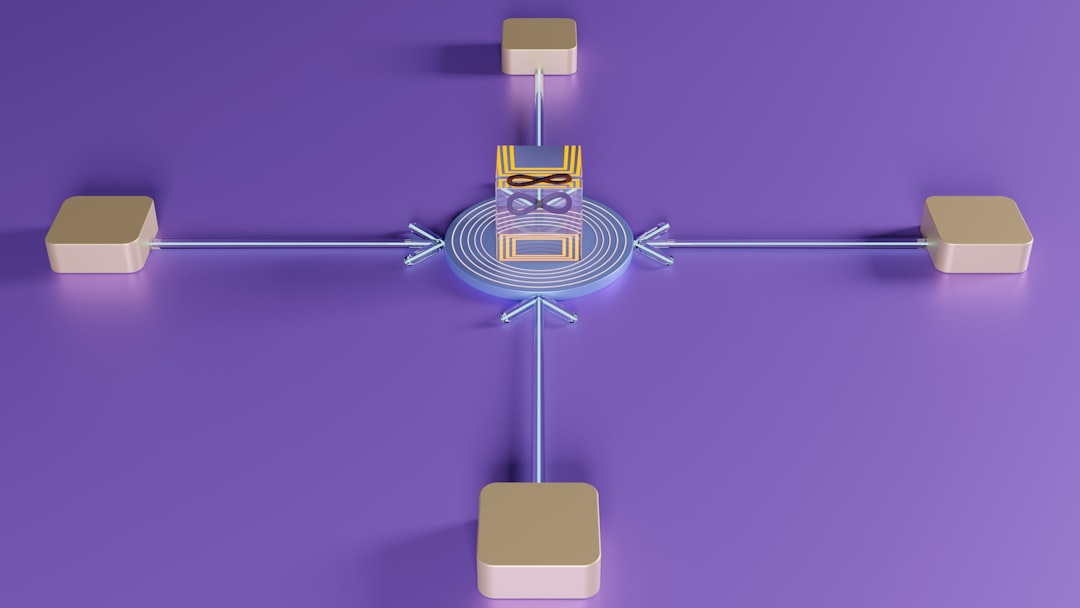
How Platforms Like Duality Work
Duality and similar platforms operationalize advanced cryptographic techniques in practical enterprise environments. Historically, homomorphic encryption was considered too slow or complex for large-scale commercial applications. However, recent breakthroughs in cryptographic efficiency and computing infrastructure have brought encrypted computation into production environments.
These platforms typically integrate:
- Fully or Partially Homomorphic Encryption for arithmetic and logical operations.
- Secure Multi-Party Computation (SMPC) for collaborative analytics between untrusted parties.
- Hardware-based trusted execution layers where appropriate.
- Access control and key management systems aligned with enterprise compliance frameworks.
Rather than forcing organizations to redesign analytics pipelines from scratch, platforms like Duality offer APIs and toolkits that integrate with existing data science workflows. Data scientists can often execute familiar models—such as regression, statistical analysis, and certain machine learning processes—on encrypted datasets with minimal workflow disruption.
Why This Matters Now
There are three converging forces driving interest in encrypted computation:
- Regulatory Pressure – Privacy laws are becoming stricter and more enforceable worldwide.
- Cybersecurity Risk – Data breaches are costly in financial and reputational terms.
- Cross-Organizational Collaboration – Businesses want to collaborate on data insights without sharing raw data.
For example, consider financial institutions seeking to detect fraud patterns across multiple banks. Traditionally, raw transactional data would need to be pooled into a shared database—creating immense privacy and antitrust concerns. With encrypted computation, each institution can keep its data encrypted locally while contributing to a joint analytical model.
The same model applies in healthcare, where research organizations can compute on encrypted patient data from multiple hospitals without exposing protected health information.
Industry Applications
Financial Services
Banks and insurance providers manage some of the world’s most sensitive datasets. Encrypted computation enables:
- Cross-bank fraud detection
- Risk modeling on consortium data
- Private credit scoring analytics
- Regulatory reporting with minimized exposure
Healthcare and Life Sciences
Medical research thrives on pooled patient data, but privacy regulations restrict sharing. Encrypted analytics allows:
- Collaborative clinical research
- Genomic data analysis
- Pharmaceutical trial assessments
- Population health modeling
Government and Defense
Public sector agencies require secure information sharing across jurisdictions and departments. Computing on encrypted intelligence datasets reduces insider threats and cross-agency vulnerabilities.

Security Advantages Over Traditional Models
Encrypted computation does more than reduce risk—it alters the threat landscape entirely.
- Minimized Attack Surface: Since raw data is never decrypted in shared environments, attackers cannot easily extract usable information.
- Reduced Insider Risk: Internal analysts work with encrypted representations rather than sensitive plaintext records.
- Stronger Compliance Posture: Demonstrating that sensitive data remains encrypted during processing can simplify audits and regulatory reviews.
- Secure Data Monetization: Organizations can derive value from datasets without directly selling or exposing the underlying information.
This architectural shift reflects a broader principle known as zero trust data security, where no system component is inherently trusted with plain data by default.
Performance and Practical Challenges
While promising, encrypted computation platforms are not without constraints. Homomorphic encryption introduces computational overhead compared to traditional processing. Although modern implementations have become dramatically more efficient, certain complex machine learning models or extremely large datasets may require optimization strategies.
Common considerations include:
- Increased compute resource requirements.
- Careful workload selection for encryption suitability.
- Specialized cryptographic expertise during deployment.
Platforms like Duality mitigate these barriers by abstracting cryptographic complexity behind enterprise-grade interfaces. The goal is not to turn every data analyst into a cryptographer, but to embed cryptographic security into familiar analytical tools.
Strategic Implications for Enterprises
Privacy-preserving computation is increasingly viewed not merely as a defensive measure, but as a strategic enabler.
Organizations adopting encrypted computation platforms can:
- Unlock Data Collaboration – Share insights without sharing source data.
- Accelerate Innovation – Access broader datasets securely.
- Increase Customer Trust – Demonstrate responsible data stewardship.
- Future-Proof Infrastructure – Align systems with evolving privacy expectations.
As artificial intelligence systems depend on increasingly diverse datasets, privacy-preserving computation may become foundational to AI governance. Enterprises that establish secure encrypted computation pipelines gain an advantage in scaling AI ethically and compliantly.
Comparing Approaches to Data Privacy
It is important to distinguish privacy-preserving computation from related techniques:
- Anonymization: Attempts to remove identifiers, but can be reversed through re-identification attacks.
- Tokenization: Replaces sensitive elements with placeholders, yet may not support complex analytics.
- Secure Enclaves: Protect data during execution but still require decryption within trusted hardware.
- Encrypted Computation: Keeps data encrypted even while operations are performed.
Encrypted computation provides one of the strongest cryptographic guarantees because the underlying raw data is mathematically protected throughout the process.

Building Trust in a Data-Driven Economy
Trust is becoming one of the most valuable currencies in the digital economy. High-profile data breaches and misuse incidents have eroded public confidence. Businesses that invest in demonstrable privacy infrastructure send a signal—to regulators, partners, and customers—that security is not an afterthought.
Platform providers like Duality position themselves as infrastructure partners rather than experimental vendors. Their focus on compliance alignment, scalability, and enterprise integration signals that encrypted computation is transitioning from academic theory into durable commercial architecture.
Critically, encrypted computation does not eliminate the need for governance policies, access controls, and monitoring. Instead, it strengthens them. Effective deployments combine:
- Robust cryptographic key management.
- Transparent audit trails.
- Defined data usage policies.
- Cross-functional security oversight.
The Road Ahead
The future of computing will not be defined solely by speed or model complexity, but by secure scalability. As data volumes grow and regulatory frameworks tighten, organizations that rely exclusively on perimeter defenses will face increasing operational risk.
Privacy-preserving computation platforms represent a structural evolution in how data is handled. Instead of asking, “How do we protect data once it’s exposed for processing?” the question becomes, “How do we design systems where exposure is unnecessary?”
As performance improvements continue and developer tooling matures, encrypted computation is likely to integrate deeply into cloud services, AI platforms, and cross-industry consortiums. Forward-looking enterprises are already piloting these technologies in high-value, high-risk areas such as fraud detection, collaborative research, and sensitive analytics.
In conclusion, platforms like Duality exemplify a critical shift toward computation models that prioritize privacy by design. By enabling analysis on encrypted data, they reduce systemic risk, support regulatory compliance, and unlock secure collaboration opportunities. As the global economy becomes ever more data-driven, computing without compromising confidentiality may well become the defining standard for responsible digital infrastructure.
